There are many ways to establish a secure SSH connection via PuTTY to a Linux-based server. Majority and the most basic method out there is using a username and password authentication. However, this is prone to dictionary attack via brute force, that’s why sites like AWS (Amazon Web services) and some others uses Public and Private key exchange. If you need to connect to a server that only accepts public keys for SSH connection this is a step-by-step tutorial on how to use PuTTY to establish a secure connection via Public keys. The idea is to let the server store a public key, and your computer (PuTTY) client will provide a private key to the server for authentication.
Prerequisites
- assuming you already created a pair of the public and private key. You’ve already added the public keys to authorized_keys on a Linux server
- you have an RSA private key as a result of the public and private key self-generated key pair
This tutorial will not convert on how to generate a pair of public and private keys. Because PuTTY doesn’t understand the id_rsa private key we need to convert the private key to a putty client format in .ppk
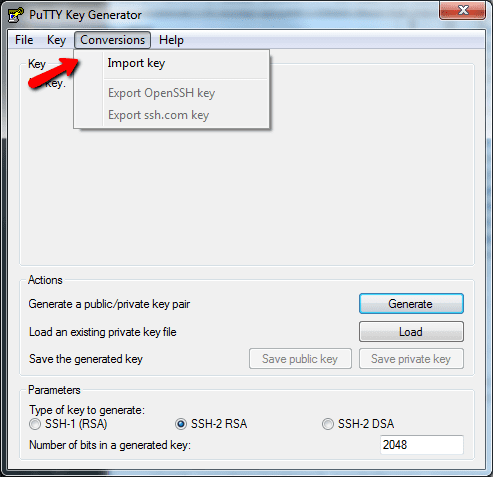
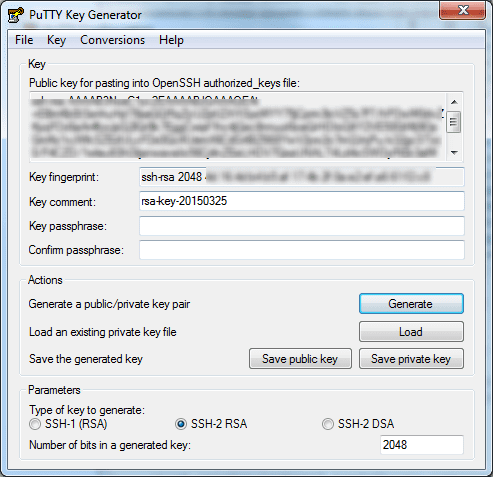
First, you need to download this utility called PuTTYgen. Launch the utility and click Conversions > Import key
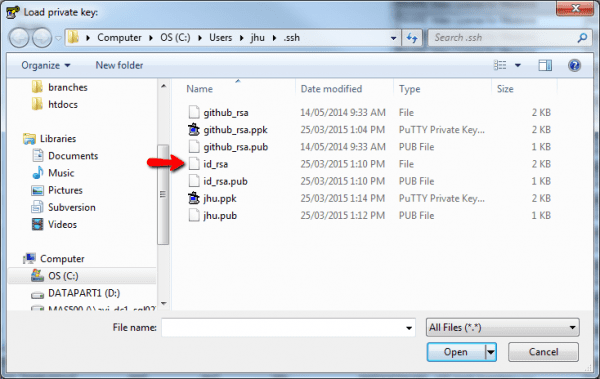
Select the id_rsa private key
It will load the id_rsa private key if you have imported the wrong format or a public key PuTTYgen will warn you for the invalid format. Click “Save private key” to finish the conversion.
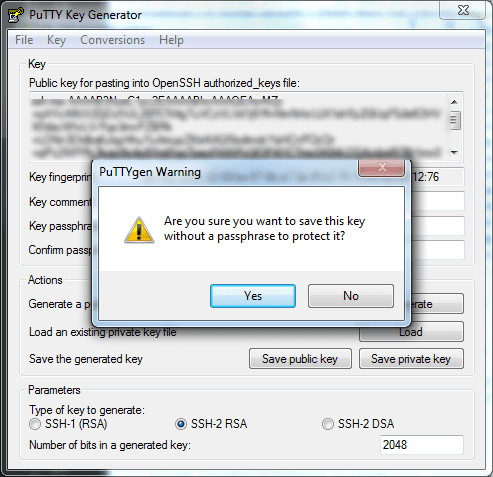
If you receive a prompt for left passphrase protect empty accept Yes, or go back to add a passphrase.
Now go back to PuTTY. Navigate the left side Category > Connection > SSH > Auth
Browse and select the .ppk you just converted under “Private key file for authentication”
Now when you go back and connect to the server, you only need to enter the username and the server IP/hostname. It will no longer prompt for your password. You will also see a message saying something like Authenticating with public key “imported-openssh-key”. This is it, you’ve just established an SSH secure connection to a server without any password. It’s important to know that the computer where you store your private key is a private computer, keep the private key in a safe location.


do you know why, for me, it is stuick on Authenticating with public key “imported-openssh-key” ? Thanks.
It helped me. Thanks